US Government Cyber Spending
In the current, austere federal budget environment, cyber spending offers a rare opportunity for business growth.
Avascent Analytics presents its Cyber Market Toolkit (beta edition) to help federal contractors identify market trends and fill a key data gap for strategic planners.
Analyzing the cyber market is one of the most challenging strategy tasks facing government contractors today. Cyber remains a growing market—a rarity in today’s austere budget environment—but with so much of the funding funneled through classified channels or hidden within larger projects, it’s easy to misjudge the amount of money in play. The Department of Defense (DoD) announced in March that its fiscal year 2015 budget request protected $5.1 billion in cyber-related funding, despite cuts to many other programs.1
Cyber remains a growing market…but with so much of the funding funneled through classified channels or hidden within larger projects, it’s easy to misjudge the amount of money in play.
But nowhere in the volumes of justification documents does the Department itemize this sum, or explain how it is distributed among various accounts, agencies, or programs.
Avascent Analytics’ US Government Cyber Market Toolkit (beta edition2) aims to quantitatively illuminate the cyber market and identify spending trends through rigorous analysis of open-source information and interviews with industry professionals. Avascent seeks to fill a critical niche in government contractors’ strategic planning needs: an entirely unclassified means of evaluating the parameters of a market that is of increasing interest, but which can be impenetrable by standard analytical methods. This paper draws on Avascent’s own knowledge base and the research used to generate the US Government Cyber Market Toolkit. What follows is an examination of key trends across future growth, customers, and market segments.
The military services are also remarkable for their growth in spending on cyber weapons…
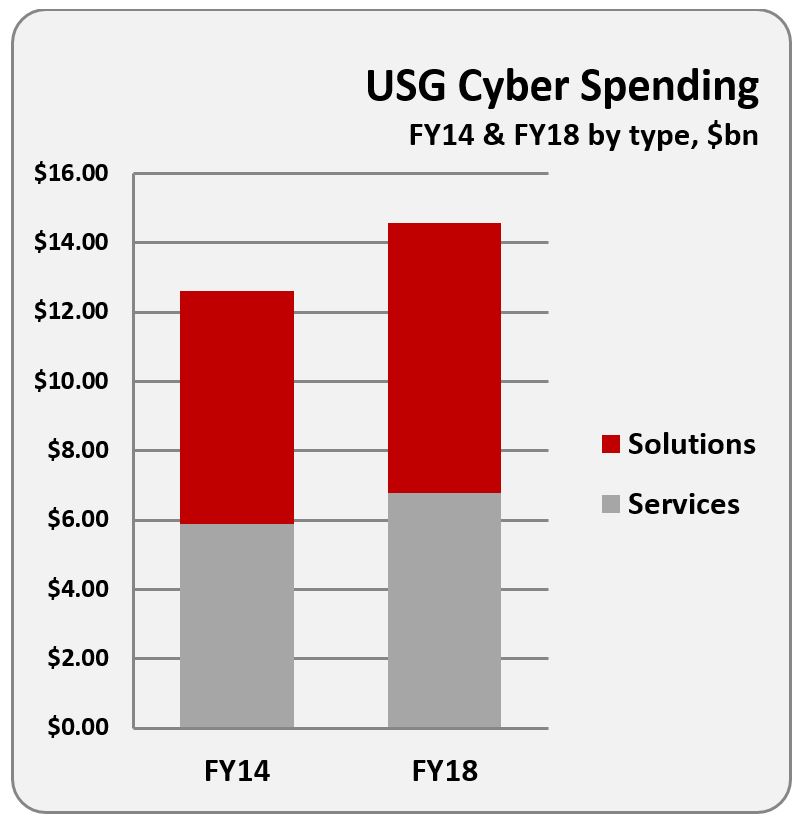
Interest in the cyber market remains strong largely due to its steady growth. Avascent expects that overall cyber spending will grow at 4% from 2014-2018. By contrast, the Budget Control Act projects almost no growth in National Defense accounts between fiscal years 2014 and 2019. Established centers of cyber investment, like the National Security Agency (NSA), will continue to feature growing demand despite their maturity as customers. However, it is customers that have not historically attracted close attention from contractors—Missile Defense Agency (MDA), Department of the Treasury, and Department of Homeland Security (DHS)—that will truly shape emerging opportunities as they procure solutions and services to harden themselves against intruders.
The military services are also remarkable for their growth in spending on cyber weapons as the component commands of US Cyber Command build capability to support operations in cyberspace. Cyber growth is also occurring at organizations that historically spent less on contractors, with strong growth expected at the National Reconnaissance Organization (11% increase from FY14 through FY18), the Navy (9%) and the FBI (8%).
Market Segmentation
US Government customers have a variety of ways to invest in cyber. The Cyber Market Toolkit incorporates broad divisions of customer spend by segmenting the market in terms of missions and functions. Cyber spending is grouped into one of two mission segments: Cyber Defense or Cyber Offense. Cyber Defense encompasses a range of activities from the preventative (e.g., continuous monitoring) to more responsive activities such as security operations centers or post-incident forensics. Cyber Offense incorporates activities to exploit adversary networks or weaponize cyber tools.
Avascent further divides the two mission segments into two functional segments: Solutions and Services. Simply put, Solutions spending covers procurements that principally involve the delivery of hardware, software or an integrated system to the government customer. By contrast, Services spending covers programs where the contractor is providing staff to augment government employees.
Government contracting trends for Solutions can cause additional confusion regarding the distinction between Solutions and Services. Several government customers have increasingly structured Solution contracts such that the contractor is only providing skilled labor and the government customer itself acts as the prime integrator or solutions designer. While these kinds of programs may seem similar to Services contracts, Avascent counts them as Solutions due to the end goal of the contract relying on the delivery of a product or system to the customer.
Presumably the ark of contracting preferences may swing back allowing contractors to provide product, rather than just labor, at these customers. Avascent’s Cyber Toolkit remains agnostic to the contracting preferences of customers. Notably, contractors interviewed suggested that contracting preferences for some customers are putting downward pressure on margins for some Solutions contracts.
Comparatively, spending on Solutions is set to slightly outpace Services across the cyber market through FY18. Customers are being driven by the need to automate cyber functions and overcome constraints in the supply of skilled labor. For example, at DHS, where new, continuous monitoring initiatives are coming online, Solutions spending is expected to rise from $300 million in FY13 to over $400 million in FY18.3
Customers
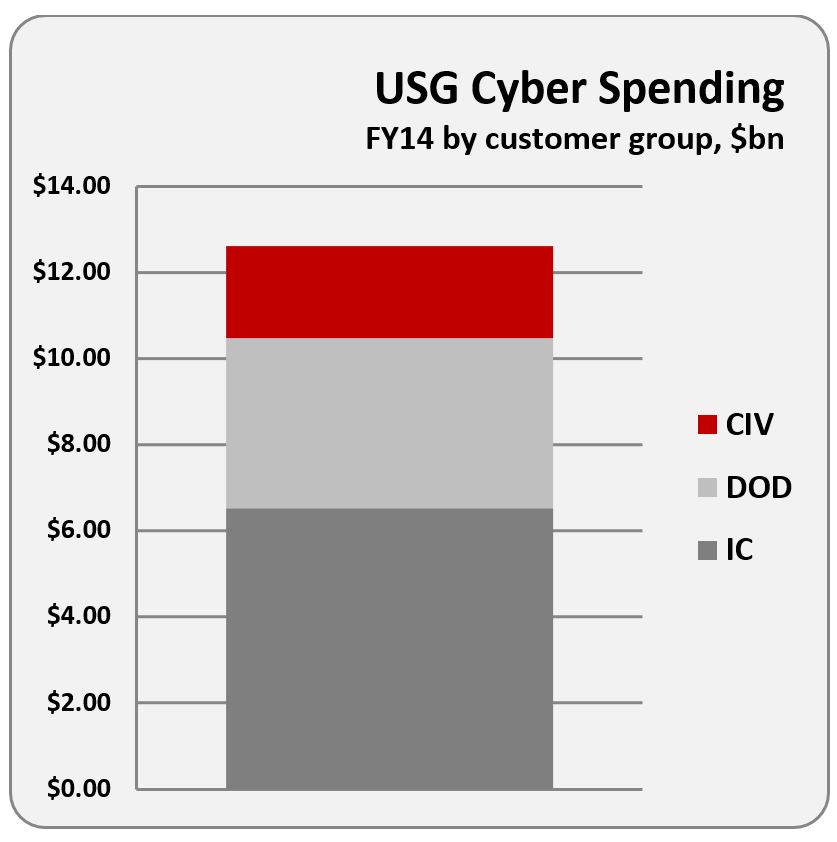
The cyber market encompasses a wide range of potential customers, from deeply classified organizations in the intelligence community to compliance-focused customers in the federal civilian agencies. The Intelligence Community continues its robust investment in cyber, with classified cyber spending from IC customers accounting for approximately 50% of total cyber spending across the US Government.
The Intelligence Community continues its robust investment in cyber…Topline funding steadily increases from roughly $6.4 billion in 2014 to almost $7.8 billion projected for 2018.
Topline funding steadily increases from roughly $6.4 billion in 2014 to almost $7.8 billion projected for 2018. A significant portion of IC spending remains focused on computer network operations and exploitation of adversary networks, with the NSA and Central Intelligence Agency (CIA) garnering the lion’s share of these budgets.
Cyber remains a relatively well-funded mission within the DoD as well. The military services—particularly the US Air Force—continue spending heavily on tradecraft and weaponized cyber. That said, the dynamic cyber threat environment also preserves funding for defensive operations, including security spending attached to large IT operations such as the Navy’s NGEN contract. The Defense Department also provides additional funding for supply chain security and measures to protect sensitive data for kinetic weapons programs, which especially benefits the MDA and major procurement programs such as the Joint Strike Fighter.
Federal Civilian customers can be divided into two categories. Security and law enforcement organizations such as DHS’ National Programs Protection Directorate (NPPD) and Federal Bureau of Investigation (FBI) have a strong spending base—collectively just under $1 billion by FY18. Large procurements, such as the DHS DOMino program, drive spending at marquis customers. However, a significant amount of spending exists across the broader Federal Civilian customer landscape, although often procured in smaller amounts. Smaller customers tend to focus heavily on compliance activities, with spending driven largely by changes in fundamental architecture (such as a shift to cloud computing or implementation of continuous monitoring). Surprisingly, the Department of Health and Human Services (HHS) is only projected to spend $235M on security in FY18—a further indication of their cavalier mentality despite the growing importance of IT in healthcare.4
Methodology
Avascent Analytics’ US Government Cyber Market Toolkit is built on both unclassified documentation and our own analysis of open source materials on classified cyber spend.
Avascent Analytics’ US Government Cyber Market Toolkit is built on both unclassified documentation and our own analysis of open source materials on classified cyber spend. Interviews with customers, contractors and industry experts help to inform every aspect of the Toolkit.
The unclassified spending portion of the Toolkit relies heavily on Avascent’s analysis of the OMB IT Schedule 53 document released each year, as well as the DoD Budget. By identifying cyber-relevant programs in the OMB IT Schedule 53 and determining the appropriate level of contractor-addressable spending in each program, we have been able to tease out growth trends across mission areas and cost types. For mission-specific cyber spending (i.e. cyber spending that is not associated with a network or IT program), Avascent analyzed DoD budgets for spend funded through RDT&E, Procurement or O&M accounts.
Classified cyber spending cannot be estimated by targeted, program-by-program analysis given the lack of public information. To estimate classified spending, Avascent maintains a proprietary, unclassified resource—the IC Market Toolkit—which estimates contractor addressable spending from the National Intelligence Program (NIP) and Military Intelligence Program (MIP). The IC Market Toolkit, a sister product to the Cyber Toolkit, is functionally segmented across the entirety of classified spending and built exclusively on open-source materials gathered from disclosures and Avascent’s own research. Cyber-relevant spending is estimated from total classified spending providing a mutually exclusive and collectively exhaustive look at cyber spend by classified customers.
NOTES
- Defense Department FY15 Budget Overview briefing, March 5, 2014, p.7.
- All data supporting the toolkit will be refreshed in May 2014, thus delivering the updated product.
- Spending totals incorporate all DHS entities, not just the NPPD organization.
- For additional information on Avascent’s IC Market Toolkit, please contact our team.





